
Security Surveillance
Security has become vital part of human life No Matter, you are at home, office or Public area. We provide Complete Customized Security Surveillance Solution for Home, Group Housing, Corporate office, Small Business, City Surveillance or Public area along with Automated Services.

Structured Cabling
A network connects multiple electronic devices with the help of cable or wireless devices. These electronic devices can be router, switches, wireless access points & I/O devices. As per the requirement.We provide cable installation services like, Ethernet cable installation services, fibre optic cabling services, data centre cabling and structured cabling services.

Switching
To connect any device to Server, there must be Connection between Receiving and Sending Device, Structured Cabling or Wireless media can give only Physical Connectivity, but how Data will transfer from one point to another point throughout end to end Point. To provide resources available for all users with single Connection, that can be done with Good Switching Solution.
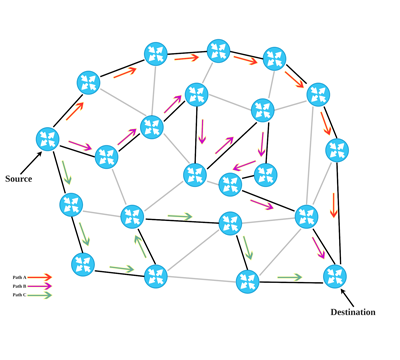
Routing
Transferring Data from one Network to another network, there are many ways or Network Path, but which one is best and Secure, to accomplish task Routing Play Vital Role. Best routing Protocol along with Automated Configurations Can provide Good Solution only.

Network Security
Data is everything for Human being, Data are travelling one point to another Point by crossing number of electronic Device. There are many software or Devices are being used by hackers to steal information. To Protect Data, We provide end to end Date Security Solution along with Hardware or Software Configurations.
